Software patches are concise, targeted updates that fix bugs, close security gaps, and often enhance functionality. They represent a disciplined approach to software maintenance, delivering fixes without unnecessary downtime. These changes are incremental, designed to improve stability and reliability while adapting to a changing environment. Careful testing and staged deployment help minimize disruption to users when applying patches. Understanding how and when to deploy responsibly is essential for maintaining security and performance in modern IT environments.
In plain terms, ongoing updates act as threat fixes and maintenance tasks that harden systems against evolving risks. From a risk-management perspective, the practice is known as patching, remediation, or update deployment, and it fits within patch management. LSI-friendly terms such as vulnerability remediation, version control, and change management help teams grasp the broader context of this activity. Effective patching strategies emphasize visibility, testing, automation, and measured rollout to minimize downtime and maintain overall system health.
Understanding Software Patches: Purpose, Security, and Performance
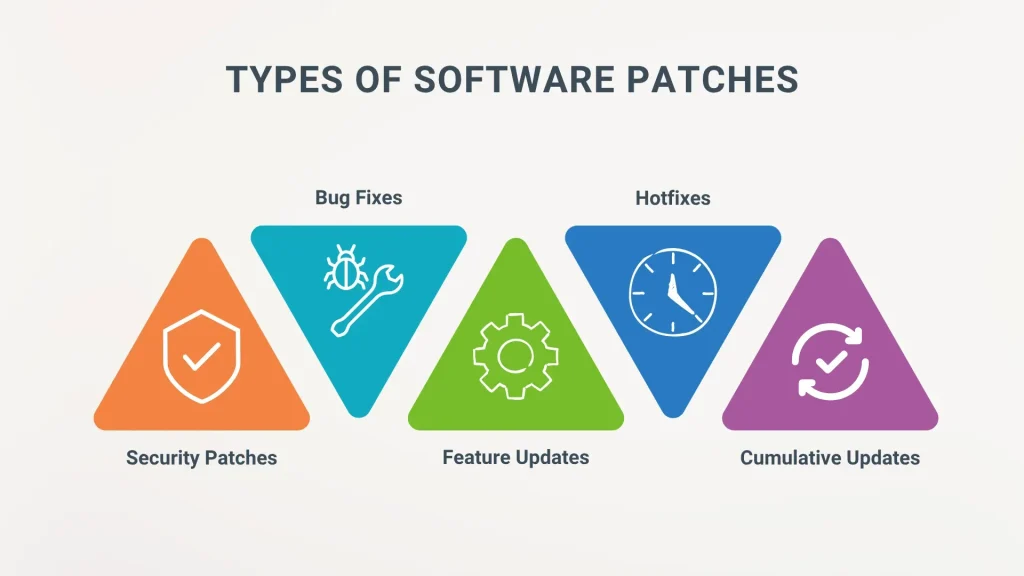
Software patches are small, targeted updates designed to fix defects, close security gaps, and sometimes improve functionality. They can be security patches that address vulnerabilities or non-security patches that enhance reliability or add features. Regardless of type, patches are incremental updates that keep software aligned with a changing environment, and they sit at the heart of effective patch management programs.
Applying patches is a foundational practice within patch management, helping teams strengthen security and improve performance. When patches address security vulnerabilities, exposure to attackers shrinks; when software updates optimize code paths and fix memory leaks, users benefit from faster, more stable experiences.
Patch Management Essentials: From Discovery to Deployment
Effective patch management starts with a comprehensive inventory of software and hardware assets. By mapping each asset to known vulnerabilities and available patches, organizations can prioritize remediation with a risk-based approach, focusing on systems that matter most to the business.
Beyond discovery, testing in isolated environments reduces the risk of deploying problematic updates. A staged deployment, clear rollback plans, and governance around patch cycles help ensure timely software updates without surprising downtime.
Addressing Security Vulnerabilities with Timely Updates
Security vulnerabilities are the primary driver for patching within mature patch management programs. When vulnerabilities are disclosed, threat actors race to exploit them, so timely patches reduce the window of opportunity for attackers.
Regular software updates also support compliance and compatibility with security controls, ensuring that defenses remain effective as the IT stack evolves. Within patch management, a mature approach ties vulnerability management to routine patch cycles and ongoing monitoring.
The Role of Zero-Day Patches in Rapid Incident Response
Zero-day patches tackle flaws that have little to no prior warning, requiring rapid evaluation and emergency deployment. In many cases, vendors provide temporary mitigations while a patch is prepared to reduce immediate risk, all within a disciplined patch management framework.
An effective patch program within patch management defines escalation paths, automation options, and testing procedures that balance speed with system stability. Even under pressure, you should verify outcomes and monitor performance impacts to protect security and reliability.
Balancing Security and Performance Through Thoughtful Patch Strategy
Balancing security and performance means weighing the security gains from patches against possible performance changes within patch management. Some patches optimize memory management or resource usage, while others may introduce compatibility tweaks that require testing in staging environments.
A risk-based cadence, regular maintenance windows, and rollback capabilities help maintain performance and availability while closing critical vulnerabilities. Telemetry and metrics on patch adoption and post-patch performance inform continuous improvement.
Practical Tools and Best Practices for Effective Patch Management
Practical patch management relies on the right tools. Windows environments commonly use WSUS or SCCM for centralized patch deployment, while Linux ecosystems rely on package managers and automation platforms like apt, yum/dnf, Ansible, or Puppet.
Core best practices include building a software bill of materials (SBOM), integrating vulnerability scanning with patch deployment, and maintaining an auditable patch history. Automation, visibility, and measurable outcomes—such as patch adoption rates and post-patch security and performance improvements—drive sustained resilience within patch management programs.
Frequently Asked Questions
What are software patches and why is patch management important?
Software patches are small, targeted updates that fix defects, close security vulnerabilities, and often improve functionality. They form the core of patch management and are essential for maintaining security and performance across the software stack.
How often should organizations apply software patches to minimize exposure to security vulnerabilities?
Use a risk-based cadence: prioritize critical patches, test them in non-production environments, and deploy through a controlled patch management process. Timely application of patches reduces exposure to security vulnerabilities and keeps systems secure and up to date.
What is the difference between security patches and non-security patches, and how should they be prioritized?
Security patches specifically address vulnerabilities, while non-security patches improve reliability or add features. In patch management, prioritize patches based on risk, impact, and exposure, with zero-day patches receiving the fastest attention.
What are zero-day patches and how should I respond in patch management?
Zero-day patches fix vulnerabilities that are exploited before a fix is available. With zero-day patches, organizations should accelerate evaluation and deployment within the patch management workflow, using compensating controls if immediate patching isn’t possible.
How do software updates relate to security and performance?
Software updates often close security vulnerabilities and can improve performance and reliability. Balance security gains with potential performance changes by testing updates and following a disciplined patch management process.
What practical steps can strengthen your patch management program against security vulnerabilities?
Build a reliable asset inventory and SBOM, apply a risk-based patching schedule, integrate vulnerability scanning, test patches, automate deployment, and monitor outcomes. These steps strengthen patch management and reduce exposure to security vulnerabilities.
| Aspect | Key points |
|---|---|
| What are patches? | Incremental updates to fix defects, mitigate security risks, improve reliability or add features. They can be security patches, non-security patches, or a mix. |
| Why patches matter for security | Close vulnerabilities quickly to reduce the attack surface; maintain compatibility with security controls; support compliance; shorten the risk window. |
| Patches and performance | Can optimize code paths, fix memory leaks, reduce crashes, and improve resource management. Requires testing; performance impact can vary. |
| Patch management lifecycle | Discovery, vulnerability assessment, testing, deployment, verification, rollback/contingency. |
| Keys to success | Prioritize critical patches, establish maintenance windows, use automation, test in non-production, monitor outcomes. |
| Challenges and myths | Downtime concerns, compatibility issues, patch fatigue. Patching is essential for all organizations, not optional. |
| Zero-day patches | Urgent fixes with rapid evaluation and deployment; use compensating controls when immediate patching isn’t feasible. |
| Tools and strategies | Windows: WSUS/SCCM; Linux: apt/yum/dnf; automation: Ansible, Puppet; integrated solutions provide visibility and control. |
| Governance | Compliance, audit trails, patch status documentation, risk exposure reviews. |
| Practical steps | Asset inventory and SBOM, risk-based schedules, vulnerability scanning, test plans, rollback, automation, telemetry, transparent communication. |
| Real-world outcomes | Lower exposure to exploits, fewer incidents, and improved reliability and performance. |
Summary
Software patches are a strategic measure that strengthens security and reliability across modern IT stacks. They matter not only for closing vulnerabilities but also for maintaining performance and compatibility as systems evolve. A well-designed patch management program—combining discovery, testing, controlled deployment, and rollback plans—helps organizations reduce risk, minimize downtime, and sustain resilience in a fast-changing digital landscape.