Patch management is the disciplined process of discovering, testing, and applying software patches to fix security flaws, address bugs, and improve compatibility across diverse systems and endpoints. In modern IT environments, this approach works best when it integrates with vulnerability management to prioritize updates based on asset criticality, exposure, and exploit risk, as part of the patch management process. By aligning with patch deployment best practices and timely security updates, organizations can reduce the attack surface, shorten remediation cycles, and maintain service continuity across servers, endpoints, and cloud workloads. Automation, centralized patch management tools, and clear change controls streamline discovery, testing, rollout, and verification while minimizing disruptions. This holistic approach supports compliance, governance, and long-term IT resilience by reducing vulnerability exposure and improving visibility into patch status.
Viewed through an alternative lens, the same effort can be described as a structured software maintenance cycle that keeps applications and devices current with the latest fixes. From a risk management standpoint, update management practices resemble a continuous remediation workflow that lowers exposure through timely security fixes and reliability enhancements. Organizations speak of vulnerability mitigation, asset hygiene, and safe rollout procedures as essential elements of robust IT governance. In addition to security, these efforts align with compliance audits, reporting, and ongoing monitoring to demonstrate resilient, well-governed operations.
Patch Management Fundamentals: What It Is and Why It Matters
Patch management is the ongoing lifecycle of discovering, evaluating, testing, and deploying software patches to fix security flaws, address bugs, and improve compatibility. It spans on-premises servers, cloud services, and diverse endpoints, and it hinges on visibility, risk assessment, and coordinated action. A mature patch management approach reduces the window of exposure to known vulnerabilities and supports regulatory compliance, governance, and operational performance across the organization.
Without a disciplined patch management program, organizations face elevated risk from exploits, malware, and data breaches, as well as potential downtime due to unpatched software. By aligning patch management with vulnerability management and security updates, teams can prioritize remediation based on asset criticality, exposure, and exploitability, translating patch releases into real risk reductions across the environment.
Understanding Software Patches: Types and Their Impact on Security Updates
Software patches come in several forms, each serving a distinct purpose. The primary goal of patches is to fix security vulnerabilities that attackers could exploit, but patches also resolve bugs, improve performance, and enhance compatibility with other software and hardware. Recognizing these categories helps security teams plan and execute a more effective patch management process.
Security patches close vulnerabilities and reduce risk, making them central to vulnerability management. Bug fixes, feature patches, and driver or firmware updates each affect stability and security posture in different ways, so organizations should classify patches within their patch management process to determine urgency, testing requirements, and deployment timing, all while monitoring for any impact on security updates.
Integrating Patch Management with Vulnerability Management for Stronger Defenses
Patch management does not operate in isolation. When new patches are released, vulnerability management teams evaluate risk, determine urgency, and prioritize deployment based on asset criticality, exposure, and exploitability. This integration turns patch releases into concrete risk reductions and more reliable security updates for endpoints and servers.
A tightly coupled approach uses vulnerability scanning data to validate patch coverage and identify residual gaps. By tying patch deployment to vulnerability trends and governance metrics, organizations can demonstrate how remediation reduces overall risk, improve audit readiness, and continuously strengthen their security posture.
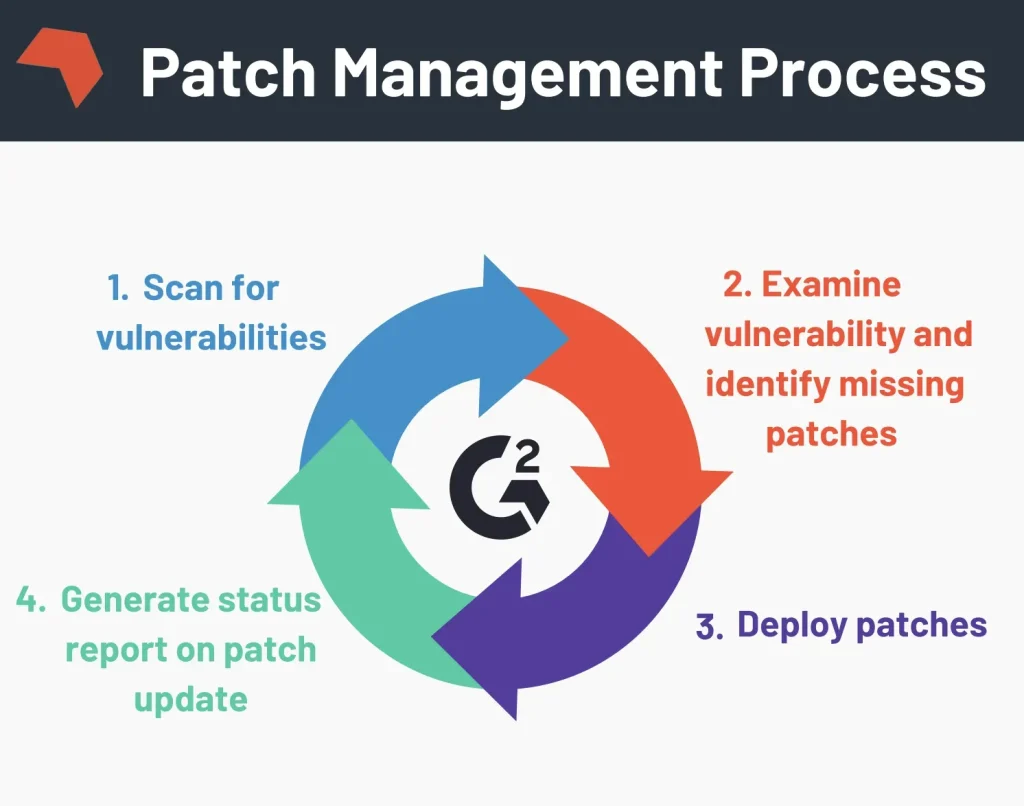
A Practical Patch Management Process: From Discovery to Verification
A practical patch management process starts with discovery and inventory to build a complete map of software, devices, and cloud assets. This visibility is essential for accurate exposure assessment and effective patching across all environments, ensuring that no component is left unpatched.
Next comes risk assessment and prioritization, followed by patch testing and staging to catch compatibility issues before broad deployment. Change management approvals, careful deployment planning, and structured verification ensure patches install correctly and do not disrupt critical applications, with ongoing vulnerability scanning to validate coverage and security updates.
Patch Deployment Best Practices: Automation, Testing, and Rollback
Patch deployment best practices emphasize automation and centralized tooling to speed up discovery, testing, deployment, and verification across operating systems, applications, and cloud services. Automation reduces manual error and ensures consistent execution of the patch management process, while monitoring tools alert teams to adverse effects in real time.
A staged rollout approach, starting with non-production systems and a limited cohort of critical devices, helps halve blast radius in case issues arise. It should be paired with a rollback plan, emergency patch windows for critical flaws, and proactive coordination with security teams and vendors to keep up with timely security updates and ongoing vulnerability management.
Measuring Patch Success: Metrics, Reporting, and Compliance
Measuring patch success involves tracking metrics such as mean time to patch, patch deployment success rate, and reductions in vulnerability exposure. Dashboards that correlate patch progress with vulnerability management results enable security teams to quantify improvements, communicate value to stakeholders, and drive continuous optimization of the patch management process.
Beyond technical outcomes, reporting supports regulatory compliance and governance. Maintaining documentation of what was patched, when, and by whom provides evidence for audits and demonstrates ongoing protection through vulnerability management dashboards and security updates, reinforcing an organization’s commitment to strong patch management discipline.
Frequently Asked Questions
What is patch management and why is it essential for vulnerability management and security updates?
Patch management is the lifecycle of discovering, evaluating, testing, deploying, and verifying software patches. It is essential for vulnerability management because timely software patches close known security gaps, reducing the window of exposure. It also supports security updates by ensuring systems stay current with vendor fixes, helping maintain compliance and operational stability.
How do patch management and vulnerability management work together during the patch management process?
Vulnerability management identifies exposed weaknesses; patch management prioritizes and deploys the corresponding software patches to close those gaps. The patch management process uses risk-based scoring to decide urgency and leverages vulnerability scanning to validate coverage. Ongoing verification reduces residual risk and strengthens security posture.
What are patch deployment best practices to minimize downtime and risk when applying software patches?
Patch deployment best practices to minimize downtime include testing patches in a staging environment, conducting phased rollouts, and having a rollback plan. Automate discovery and deployment where possible, while ensuring change-management approvals. Monitor systems during deployment and document rollback windows to limit blast radius.
What should be included in a patch management process to ensure effective software patches and timely security updates?
A patch management process should include: 1) discovery and inventory; 2) risk-based prioritization; 3) patch testing and staging; 4) change-management approval; 5) structured deployment; 6) verification and reporting; and 7) documentation and compliance. This framework ensures effective software patches and timely security updates while supporting governance and auditing.
How can you measure patch management effectiveness and its impact on vulnerability management and security updates?
Key metrics include mean time to patch, patch deployment success rate, and reduction in vulnerability exposure. Link these metrics to vulnerability management dashboards to verify coverage and identify residual risk. Regular reporting demonstrates improvements in security updates and overall risk posture.
What are common pitfalls in patch management and how can you avoid them using the patch management process?
Common pitfalls include incomplete visibility, patch fatigue, inadequate testing, improper change control, and poor communication. Avoid them by maintaining a comprehensive asset inventory, applying risk-based prioritization, following patch deployment best practices, automating where possible, testing patches in staging, and coordinating with security teams for advisories and approvals.
| Aspect | Key Points |
|---|---|
| Definition and Purpose | Patch management is the systematic approach to handling software patches—updates released by vendors to fix security flaws, address bugs, and improve compatibility. It is essential for maintaining security, compliance, and operational performance in modern IT environments that include on-premises servers, cloud services, and endpoints. |
| Patch Types |
|
| Relationship with Vulnerability Management | Patch management is an ongoing lifecycle that starts with discovering all software and devices, assessing the risk posed by missing patches, and then deploying patches in a controlled, timely manner to minimize exposure while maintaining system stability and user productivity. It helps meet regulatory requirements and supports IT governance by turning patch releases into tangible risk reductions and improved security updates for end users and systems. |
| Patch Management Process – Core Steps |
|
| Best Practices |
|
| Common Pitfalls |
|
| Tools and Solutions |
|
Summary
Patch management is a foundational discipline in modern IT security and operations. It focuses on systematically discovering software and devices, prioritizing patches by risk, validating changes in staging, and deploying updates to minimize exposure to vulnerabilities. The process emphasizes automation, governance, and clear documentation to maintain compliance and reduce downtime while supporting business objectives. By integrating patch management with vulnerability management and security updates, organizations can strengthen their security posture and ensure reliable IT services in a dynamic, multi-environment landscape.