Software patches are a backbone of modern IT hygiene, helping keep systems secure and reliable from the moment they are released. They deliver security updates, vulnerability fixes, and software updates, reducing exposure and downtime for servers, desktops, and cloud services. Effective patching relies on a disciplined process, not ad hoc installs, to balance risk with business continuity. When organizations adopt proper patch management practices, automatic updates can be harnessed safely while still allowing testing and rollback. In short, this proactive approach underpins resilience, compliance, and smoother operations across the organization.
To frame the idea in broader terms, think of it as ongoing code fixes, security remediation, and systematic software maintenance that keep programs trustworthy. Rather than waiting for major releases, teams apply small, targeted changes—often called hotfixes or patches in the broader sense—to seal security gaps and stabilize performance. This approach mirrors the language of vulnerability fixes, patch management, and automated update cycles designed to minimize risk during deployment. By mapping related concepts like software updates, automatic updates, and proactive risk assessment, organizations can optimize workflows and governance while preserving uptime. Ultimately, the goal is to maintain a resilient technology stack through timely maintenance actions that address flaws, improve compatibility, and defend against threats.
What are Software Patches and why they matter
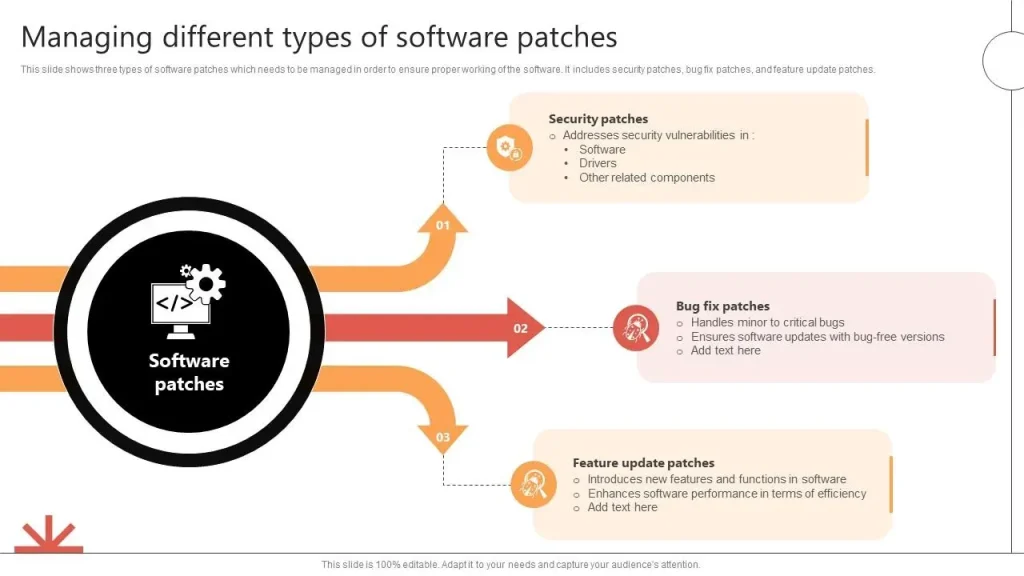
Software patches are small, targeted code fixes released after a product’s initial launch. They address security updates, close vulnerabilities, and fix defects that could cause crashes or data loss. When combined with patch management practices, patches help keep software updates aligned with security goals and reduce the attack surface.
Regular patching improves reliability, helps with compliance, and ensures compatibility with new hardware and cloud services. A deliberate approach to applying patches—inventorying assets, testing in controlled environments, and staged deployment—minimizes risk while maximizing uptime.
Patches vs updates: understanding the difference for security and reliability
Patches are typically small, focused fixes that address a specific defect or vulnerability, whereas updates are broader releases that may add features or major improvements. Patches often directly target security gaps and vulnerability fixes, while updates may include enhancements to functionality and performance.
Understanding this distinction helps security teams prioritize risks, schedule deployments, and balance operational needs with the imperative to apply critical security updates and keep systems aligned with the latest software updates.
Building a robust patch management strategy
A mature patch management program starts with an up-to-date asset inventory, risk scoring based on exposure, and policy-driven workflows that define when and how patches are applied. Centralized visibility is essential for effective patch management across desktops, servers, and endpoints.
Testing and staging are crucial to catch compatibility issues with third-party plugins and dependent applications before broad deployment. This reduces the chance that vulnerability fixes or security updates introduce disruptions in production.
Safe patch deployment: testing, rollback, and monitoring
Adopt phased rollout, pilot groups, and canary deployments where feasible to validate impact with minimal risk. A robust rollback plan—snapshots, backups, and tested uninstall paths—helps restore services quickly if issues arise.
Post-deployment monitoring and verification are essential to confirm patches installed correctly and to detect any performance regressions or security alerts. Continuous monitoring supports a stable security posture and reliable operations after applying updates.
The role of security updates and vulnerability fixes in resilience
Security updates and vulnerability fixes are critical in the ongoing cybersecurity landscape. Unpatched systems remain prime targets for attacks, making timely patching a core defense and a key component of resilience.
Prioritizing high-severity patches, aligning with compliance requirements, and maintaining audit trails for patch activity helps organizations demonstrate due diligence and reduce risk while keeping systems safe.
Automation, tools, and workflows for scalable patch management
Automation accelerates discovery, testing, and deployment across endpoints, servers, and cloud environments. Centralized orchestration reduces manual effort, speeds response to vulnerabilities, and improves consistency.
Leverage vulnerability scanners, configuration management, and software distribution platforms, and integrate with IT service management for end-to-end patch workflows. In Windows environments, examples include Windows Update for Business, WSUS, and cross-platform approaches using apt or dnf with enterprise-grade catalogs.
Frequently Asked Questions
What are software patches and how do they relate to security updates and vulnerability fixes?
Software patches are targeted code changes released to fix a specific defect or vulnerability after the software’s initial release. They address security updates and vulnerability fixes, and they are a core element of patch management. Unlike broad software updates, patches are surgical changes aimed at restoring correctness and security.
Why is patch management important for maintaining software updates and compliance?
Patch management is the structured process of discovering, testing, deploying, and monitoring patches across an organization’s IT environment. It ensures timely security updates and vulnerability fixes, reduces risk, supports regulatory compliance, and provides auditable records.
What is the difference between patches and software updates, and when should you apply each?
Patches are targeted fixes for specific issues or vulnerabilities; software updates are broader releases that may add features or improve functionality. In practice, patch management prioritizes security updates and vulnerability fixes, while software updates may deliver new capabilities.
How can you apply software patches safely without causing downtime?
Follow best practices: test patches in a staging environment, create reliable backups, implement a rollback plan, use phased rollouts or canaries, and monitor post-deployment results to verify success. This reduces risk during patch management and ensures security updates are applied without unnecessary downtime.
How do automatic updates affect patch management and security posture?
Automatic updates speed the delivery of patches, including security updates and vulnerability fixes, improving the organization’s security posture. However, they should be combined with testing, change management, and monitoring to avoid incompatibilities.
What common risks should you avoid when deploying patches?
Avoid skipping testing, neglecting dependency checks, relying only on automatic updates without validation, failing to back up and plan rollback, and overlooking critical security updates. Proper patch management and vulnerability fixes require validation and backups.
| Aspect | Key Points |
|---|---|
| What software patches are and how they differ from updates | Patches fix specific issues and vulnerabilities after release; updates are broader releases that add features or major improvements. |
| Why patches matter | Security, reliability, and compliance improvements; can enhance performance and compatibility. |
| The patch development and testing lifecycle | Discovery & assessment; development; testing/QA; staging/release; monitoring/support. Testing and phased rollouts are critical. |
| Patch management: a structured approach | Planning, testing, deploying, and monitoring patches across assets; includes asset inventory, risk assessment, testing, deployment, verification. |
| Best practices for applying patches safely | Establish policy; inventory; test in staging; rollback plan; schedule; backups; verify & monitor; prioritize security updates; automate; review & learn. |
| Tactics for safe deployment | Phased rollout, canaries, and rollback capability with monitoring. |
| Automation, tooling, and integration | Automation reduces manual effort; use configuration management tools, endpoint management, vulnerability scanners; integrate with ticketing/change-management; examples: Windows Update/WSUS, apt/dnf. |
| Practical considerations for different environments | Personal devices: enable automatic updates; small businesses: lean schedule; enterprises: governance and cross-team coordination. |
| Risks and pitfalls to avoid | Skipping testing; ignoring dependencies; relying solely on automatic updates; inadequate backups or rollback; IoT/embedded patching challenges. |
| The role of software patches in cybersecurity and resilience | Patches reduce attack surface, support compliance, and sustain resilience through ongoing discipline. |
Summary
Software patches are a critical, ongoing part of maintaining healthy IT systems, delivering security updates and vulnerability fixes while aligning with broader software updates and automatic updates strategies. A well-managed patch program—encompassing patch management, testing, staged rollouts, backups, and continuous monitoring—keeps systems protected against emerging threats and ensures regulatory readiness. By prioritizing critical fixes, leveraging automation where appropriate, and maintaining robust rollback capabilities, organizations can apply Software patches safely, minimize downtime, and preserve business continuity.